Estimated reading time: 2 minutes
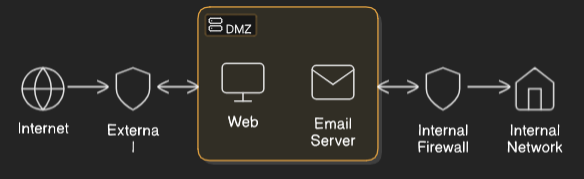
In cybersecurity, a DMZ (Demilitarized Zone) is a segmented network area that sits between an internal (trusted) network and an external (untrusted) network, typically the internet. Its primary function is to add an additional layer of security by isolating public-facing services from the internal network, reducing the risk that a compromise of those services will lead to broader internal compromise.
Technical Breakdown:
- Network Segmentation:
- A DMZ is typically implemented using firewalls and/or router ACLs to control traffic flow.
- It is often placed between two firewalls:
- One external firewall filters traffic between the internet and the DMZ.
- One internal firewall filters traffic between the DMZ and the internal network.
- Services Commonly Placed in the DMZ:
- Web servers
- Mail servers
- DNS servers
- VPN gateways
- Reverse proxies
- Any service that must be accessed externally
- Security Benefit:
- If an attacker compromises a DMZ system, they are still isolated from the internal network.
- Strict firewall rules limit lateral movement.
- Intrusion detection systems (IDS) and monitoring tools are often used within the DMZ to detect anomalies.
- Traffic Flow Example:
- A user requests data from a web server in the DMZ.
- The web server may query an internal database through tightly controlled rules on the internal firewall.
- Responses pass back through the DMZ to the user without exposing the internal network directly.
Summary:
The DMZ acts as a buffer zone, minimizing the attack surface and containing damage if public-facing services are compromised. It supports the principle of defense in depth by enforcing segmentation and access control between the external world and internal resources.